Copyright to AlphaCoders
The Rise of the Em Dash
2026-05-02
An exploration of how digital communication and LLMs are shifting our use of punctuation from formal colons to dynamic em dashes.
536 words
|
3 minutes
The Comprehension Crisis: When AI Writes Code We No Longer Understand
2026-04-11
AI tools have turned tasks that used to take days into mere hours, yet we are shipping code we don't fully understand.
971 words
|
5 minutes

The Architect's Mind: Balancing Design Patterns and Pragmatism
2026-04-08
A deep dive into the utility and pitfalls of design patterns, from classic object-oriented structures to modern distributed systems and AI-assisted orchestration.
1405 words
|
7 minutes

Enterprise VPN Implementation Strategy for 300 Users
2026-03-15
A practical architecture guide for deploying a secure, scalable enterprise VPN with WireGuard, identity controls, and high availability.
3428 words
|
17 minutes
The Great Digital Migration: Decoding the 'Real' History of Numbers
2026-03-10
A concise historical walkthrough of numeral systems, from Brahmi and Arabic transmission to Roman legacy and base-60 influence.
1185 words
|
6 minutes
The Agentic Revolution: A Deep Dive into the Tools Powering Autonomous AI
2026-03-01
An exhaustive exploration of the core frameworks and libraries that enable the development of autonomous, goal-oriented AI agents.
984 words
|
5 minutes
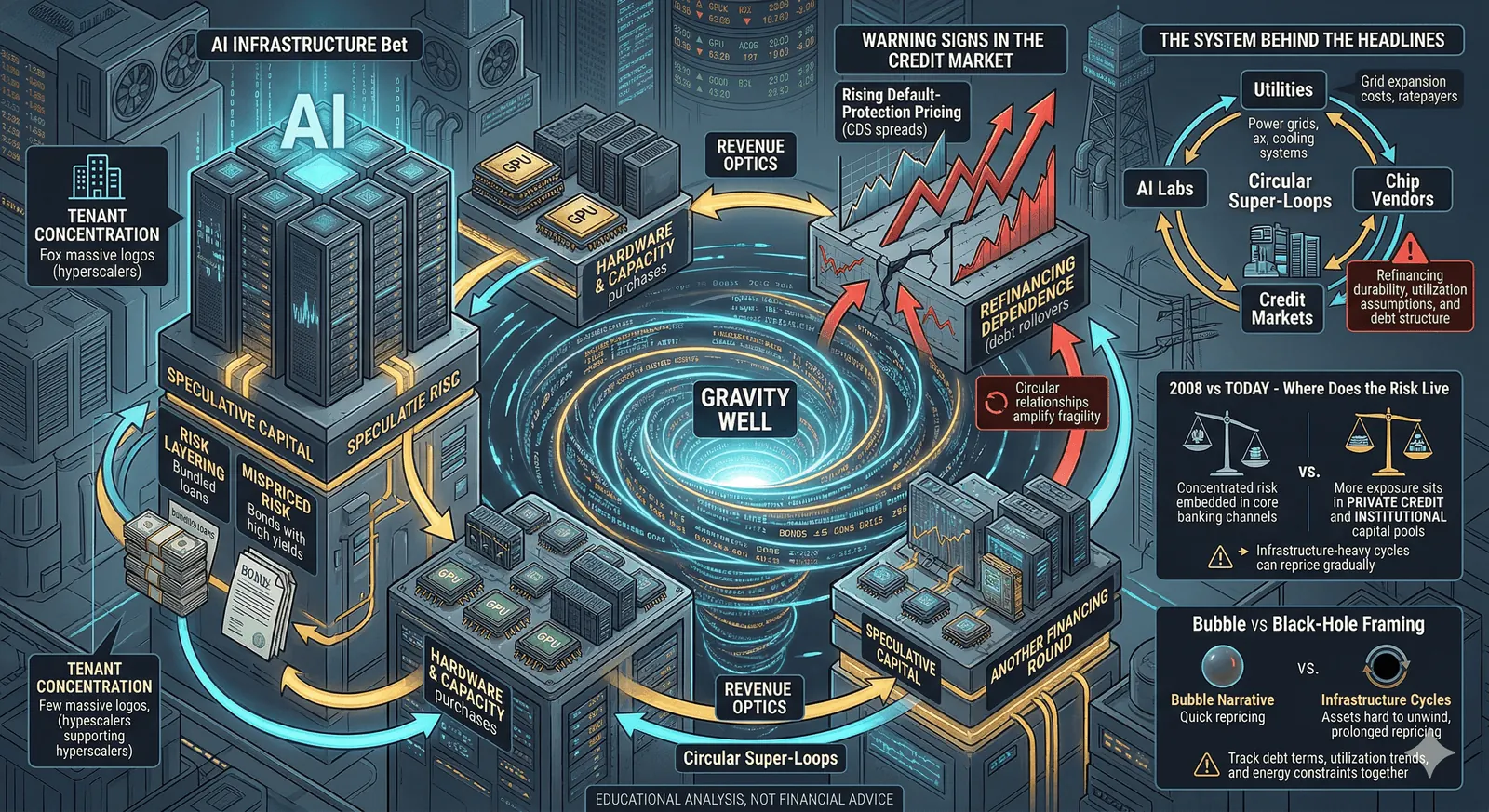
AI Capital Gravity - Parallels and Why This Cycle Behaves Differently
2026-02-12
A merged analysis of AI infrastructure financing, circular capital loops, and how current risk signals compare with the 2008 credit era.
520 words
|
3 minutes
The Kali Linux Arsenal: A Comprehensive Guide to Every Weapon in Your Pentesting Toolkit
2026-01-27
A deep dive into the industry-standard tools for reconnaissance, vulnerability assessment, exploitation, and post-exploitation.
1495 words
|
7 minutes

